Een toets heeft een stabiel object nodig
Bestuurlijke instrumenten beoordelen toestanden. Een toets, accreditatie of kader stelt vast of iets op een bepaald moment in de juiste staat verkeert, en ontleent zijn waarde aan de aanname dat die toestand stabiel blijft tot het volgende toetsmoment. Dat werkt zolang de eigenschap waar het om gaat berust op een stabiel object: iets dat zich laat aanwijzen, vastleggen en opnieuw onderzoeken. Veel eigenschappen waar beslissingen uiteindelijk over gaan, gedragen zich anders. Ze liggen niet besloten in een object, maar ontstaan in een proces, verhouding of gebruik. En die houden niet stil voor de meting. Dan komt een instrument niet tot een verkeerde conclusie, maar meet het een ander soort eigenschap dan de relevante. Niet omdat het slecht ontworpen is, maar omdat het aangrijpt op iets anders dan waar de relevante eigenschap ontstaat. ...
The part that stays strange
Any lens explains something. That is the problem with them, not the recommendation. Point a strong enough frame at a situation, and it will find its own pattern there, because a frame is built to find that pattern, and the finding feels like discovery rather than like the frame doing what it was made to do. So the fact that a lens explains a thing is almost no evidence that the lens is the right one. Every lens clears that bar. The question worth asking is narrower and less flattering: what does the situation still leave unexplained after the usual reading has done its work, and which lens, if any, picks that up. ...

The map is mostly bottlenecks
The usual way of reading the contest over resources is to look at where they are. Whose ground holds the oil, the gas, the rare earths, the cobalt. On that picture power follows the deposit, and the country sitting on the richest seam holds the strongest hand. It is the picture behind a great deal of the current talk about resource grabs, and it is wrong in a way that the talk mostly misses. ...

The centre that depends on the room
The usual way of reading power treats it as a possession. Someone holds the leverage or they do not; the troops, the money, the umbrella, the seat at the head of the table. On that picture the strong actor is the one who can hurt the others more than they can hurt back, and the others arrange themselves accordingly because they have no better option. It is a tidy model, and it is wrong in a particular way that takes a while to show. ...
A shape of European rearmament
Everyone knows by now that Europe is rearming. That part is easy to write and carries almost nothing, because “investing in defence” survives any amount of vagueness. The interesting reading sits a little lower down, in the documents that have to name things: how much money, raised in what way, spent on what, through which legal route, under whose command. Those are harder to write and harder to take back, because somebody has to act on them. Read side by side, they sketch a shape, and the shape says more than the announcements do. ...
Reading the procurement, not the press release
A policy speech says what an institution wants to be seen wanting. A procurement document records what it has agreed to pay for. The two are not the same, and the gap between them is usually the more interesting reading. A press release costs nothing to write and binds no one. A call for tender names a budget, a deadline, a set of deliverables and a contract that someone will sign and then have to deliver against. Intentions are cheap. Commitments leave a paper trail, because somebody has to do the work and somebody has to account for the money. ...

Een transparantiewet die vindbaarheid eist
Er is een gewoonte in detection engineering die een organisatie tijd kost om af te leren. Een team kijkt naar de waarschuwingen, de dashboards en de dekkingsrapporten, en beschouwt die als de plek waar detectie gebeurt. Dat is niet zo. Het is de plek waar detectie zichtbaar wordt. Het werk dat bepaalt of er iets te zien valt, gebeurde veel eerder en veel stiller, toen iemand koos wat er gelogd werd. Zonder vastgelegde gebeurtenis genereer je geen waarschuwing. De prijs van een ontbrekende log betaal je pas tijdens een incident, wanneer blijkt dat het spoor nooit heeft bestaan. ...
The stability of dysfunction
The stability of dysfunction Many discussions of large systems quietly assume that a stable system is a healthy one, and an unstable system is a sick one. Complex systems tend to violate that intuition. They can remain operational for a very long time without becoming any healthier, and they possess several mechanisms that let them do so. Normalisation is one of those mechanisms. It is not the whole story. The whole story, if there is one, is that persistence and health are different properties, and large systems are often much better at achieving the first than the second. ...
What institutions do to successful ideas
Many critiques of Agile assume something went wrong. The story is usually told as a fall from grace: a practical response to software uncertainty that then disappeared beneath ceremonies, certifications, frameworks, and consultants. There is another way to read the same history. Perhaps Agile did not fail. Perhaps it succeeded, and what happened next is simply what institutions do to successful ideas. On that reading the interesting question is not why Agile became institutionalised. It is why successful ideas so reliably do. ...
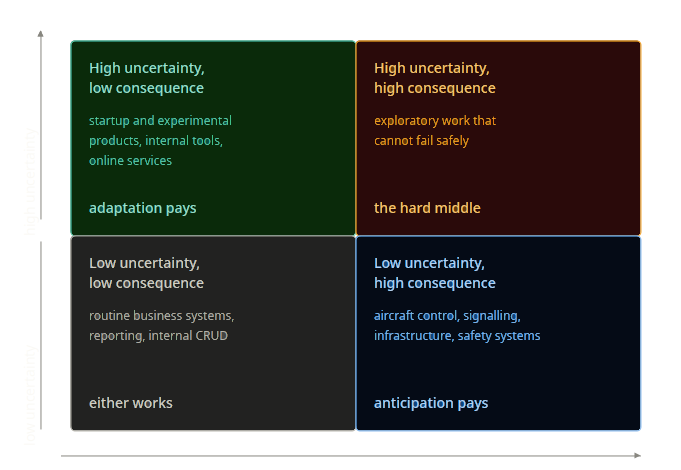
Agile, where it fits and where it doesn't
Most engineering disciplines accept that method follows from context. Nobody expects a bridge engineer, a documentary director, and a trauma surgeon to share a planning model, and nobody finds the difference remarkable. Software is one of the few fields where people go looking for a single methodology and then try to apply it to everything in sight. Agile is the most successful instance of that search, which makes it an awkward thing to argue about. The useful question is not whether it is good or bad. It is what kind of work it was meant for, and that turns out to depend on two things that have nothing to do with how much anyone likes the method. ...